Steganalysis and Machine Learning: A European answer
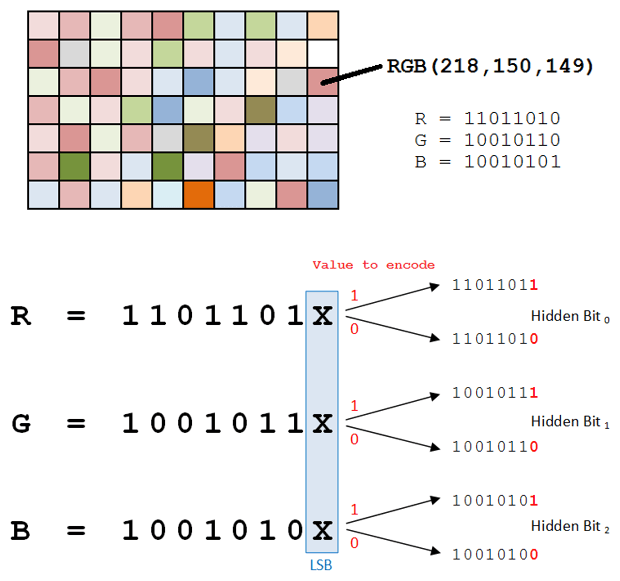
Steganography is a secret mechanism for encoding information by any means of transmission. Its use has been known since ancient Greece and defined in glossaries towards the end of the fifteenth century. Both the encoded information and the medium of transmission are secret; that is, known only to the parties who intend to communicate in an occult way. Steganography therefore presents itself as an ideal tool for the creation of secret communication channels that can be used in sophisticated espionage scenarios, computer crime and data breaches in public and private sectors.